Security
Enterprise-grade security with complete transparency.
SeCaMe is built around elaborate authorization, audited workflows, digital storage and signatures, encryption, and digitally stored documents — so procurement, finance, and operations teams can trust every approval and every cross-reference.
Security in practice
Controlled approvals, documented actions, and visible history.
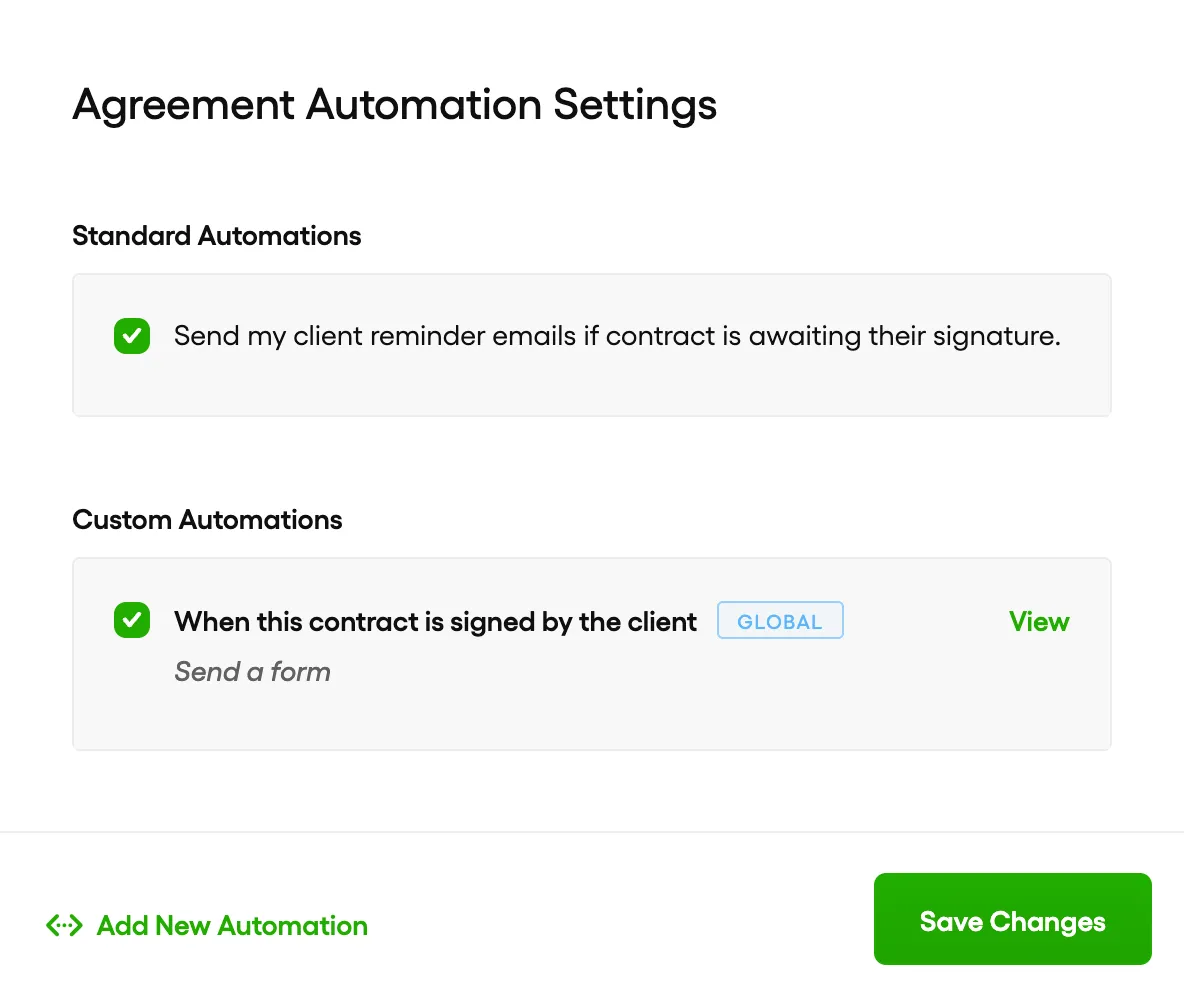
Every sensitive workflow is represented by explicit controls, automation policies, and verifiable records integrated with application global security layer.
Pillar 01
Authorization
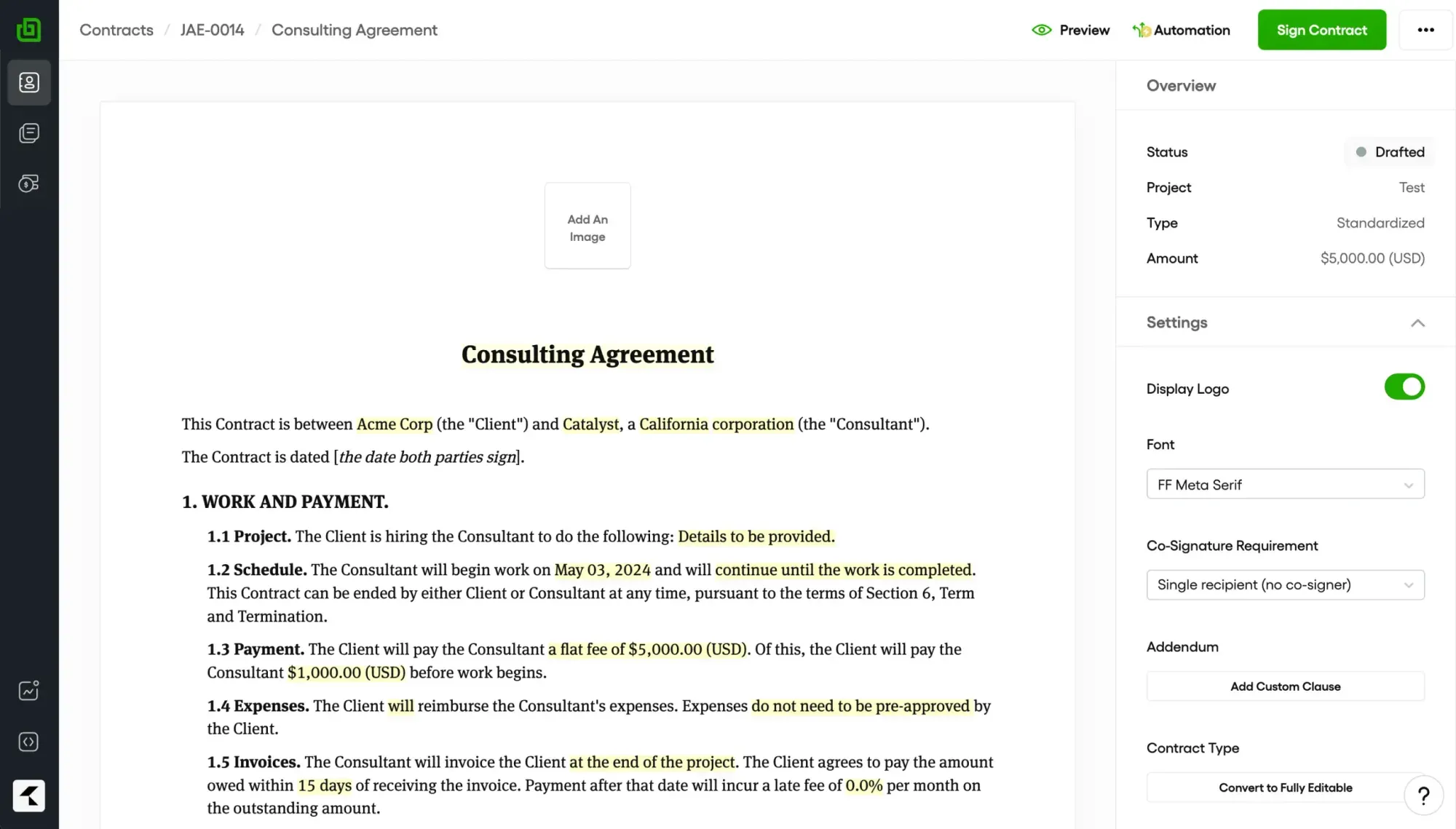
Elaborate role-based authorization governs every approval, transaction, and integration — with customizable approval flows tied to financial level and item type.
Pillar 02
Auditability
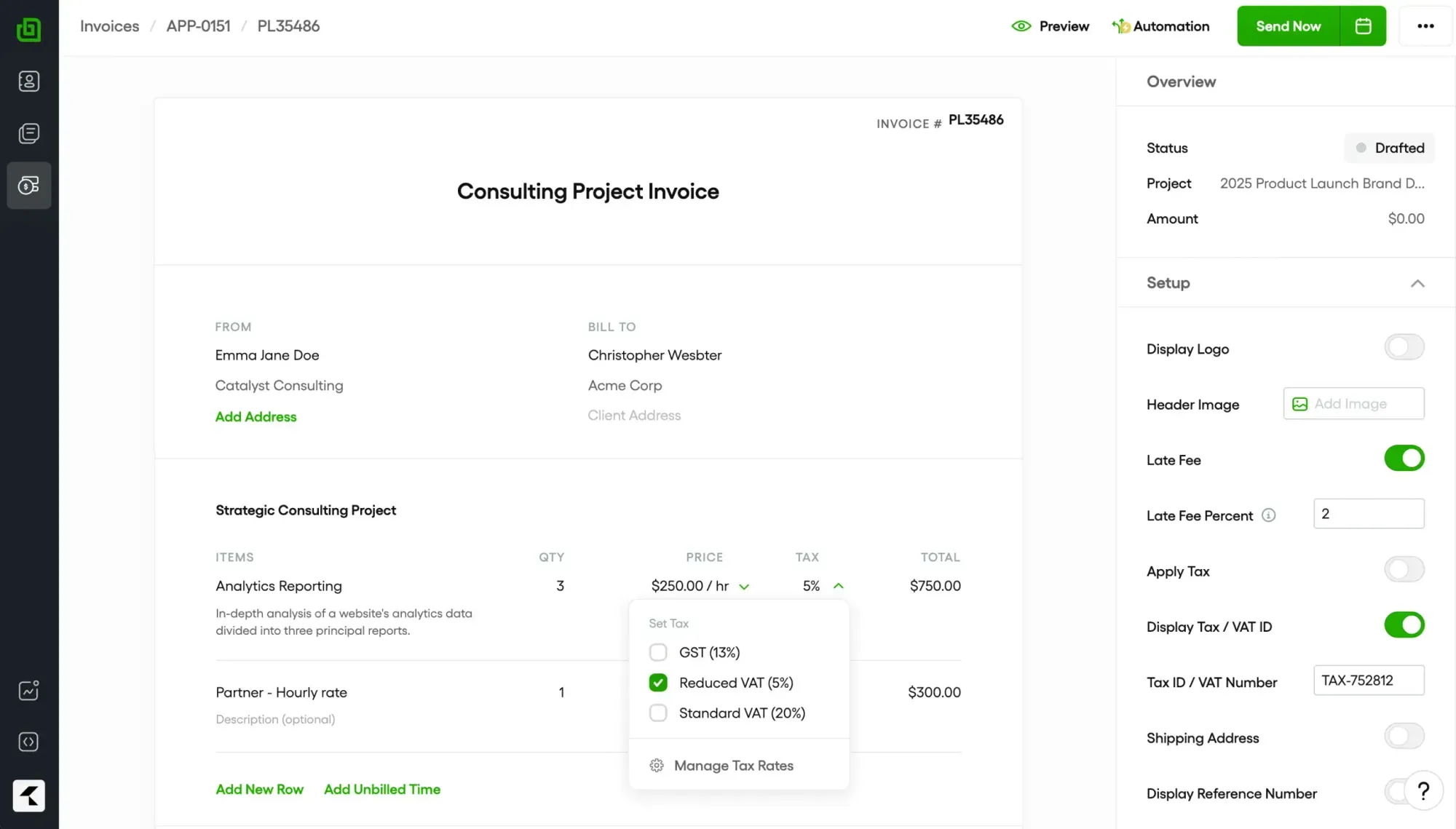
Complete transparency and auditability across the purchase-to-pay lifecycle, with digitally stored documents and cross-reference for every transaction.
Pillar 03
Platform security
SeCaMe incorporates the latest security standards and best practices, with a constant review and coverage process ensuring ongoing compliance and resilience.
Pillar 04
Data integrity
A single integrated database keeps procurement, inventory, finance, and recipes consistent — eliminating reconciliation across parallel systems.
Get started
See SeCaMe running on your operation.
Walk through procurement, inventory, recipes, and 3-way matching on a tailored dataset — guided by our team.
